The insidious Emotet botnet, which staged a return in November 2021 immediately after a 10-month-prolonged hiatus, is at the time again exhibiting indications of steady expansion, amassing a swarm of above 100,000 infected hosts for perpetrating its malicious pursuits.
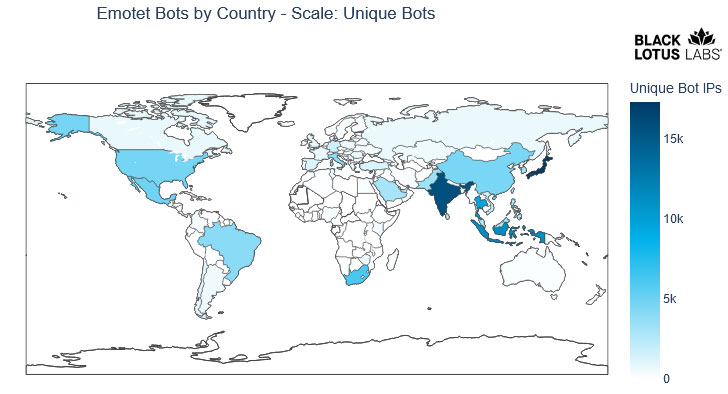
“Although Emotet has not nonetheless attained the very same scale it the moment experienced, the botnet is exhibiting a sturdy resurgence with a complete of roughly 130,000 distinctive bots unfold throughout 179 countries since November 2021,” scientists from Lumen’s Black Lotus Labs stated in a report.
Emotet, prior to its takedown in late January 2021 as component of a coordinated law enforcement procedure dubbed “Ladybird,” experienced contaminated no much less than 1.6 million gadgets globally, acting as a conduit for cybercriminals to set up other varieties of malware, these as banking trojans or ransomware, onto compromised methods.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

The malware officially resurfaced in November 2021 employing TrickBot as a delivery automobile, with the previous shuttering its attack infrastructure late final month after quite a few important associates of the group were absorbed into the Conti ransomware cartel.
Emotet’s resurrection is claimed to have been orchestrated by the Conti gang alone in an try to change practices in reaction to enhanced legislation enforcement scrutiny into the TrickBot’s malware distribution routines.
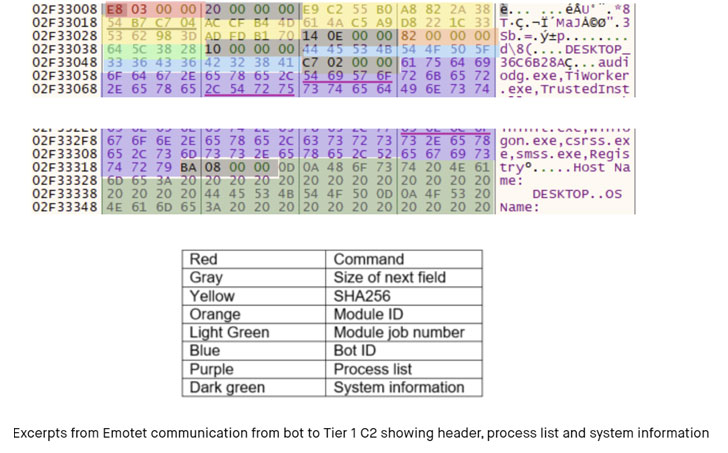
Black Lotus Labs mentioned that the “aggregation of bots actually did not begin in earnest till January [2022],” introducing the new variants of Emotet have swapped the RSA encryption plan in favor of elliptic curve cryptography (ECC) to encrypt network site visitors.
An additional new addition to its abilities is its means to get extra process information past a listing of jogging procedures from the compromised equipment.
What is extra, Emotet’s botnet infrastructure is stated to encompass nearly 200 command-and-regulate (C2) servers, with most of the domains situated in the U.S., Germany, France, Brazil, Thailand, Singapore, Indonesia, Canada, the U.K., and India.
Infected bots, on the other hand, are greatly concentrated in Asia, chiefly Japan, India, Indonesia, and Thailand, adopted by South Africa, Mexico, the U.S., China, Brazil, and Italy. “This is not shocking given the preponderance of vulnerable or outdated Windows hosts in the area,” the researchers reported.
“The growth and distribution of bots is an crucial indicator of Emotet’s development in restoring its as soon as sprawling infrastructure,” Black Lotus Labs mentioned. “Each bot is a probable foothold to a coveted network and offers an possibility to deploy Cobalt Strike or at some point be promoted to a Bot C2.”
Uncovered this short article exciting? Abide by THN on Facebook, Twitter and LinkedIn to browse far more special content we article.
Some elements of this report are sourced from:
thehackernews.com



 APT41 Spies Broke Into 6 US State Networks via a Livestock App
APT41 Spies Broke Into 6 US State Networks via a Livestock App