Password security has very long been an issue for corporations and their cybersecurity standards. Account passwords are frequently the weakest connection in the overall security posture for numerous organizations.
Numerous firms have used Microsoft’s default password insurance policies for a long time. Even though these can be custom made, companies frequently accept the default values for their corporation.
The Windows default password plan is a excellent start off, but are there security vulnerabilities affiliated with it? Let’s seem at the latest recommendations from major cybersecurity authorities and see how they measure up in opposition to the Windows default password coverage.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Windows default password policy options
Several, if not most, small business environments now use Microsoft Energetic Listing as their identity and accessibility management option in the enterprise. Lively Directory has served corporations in this capability for a long time.
Just one of the created-in abilities furnished by Microsoft Active Directory Domain Expert services (Provides) is the developed-in functionality to provide password policy for an business.
What is a password policy? A password plan provides the established of expected password characteristics that finish-end users have to meet when deciding on their account password. Below is a seem at Active Directory Default Domain Policy Password Policy configuration with standard values that many organizations may well use.
A newly promoted Windows Server 2019 Domain Controller Default Domain Group Plan exhibits the default settings for Password Policy.
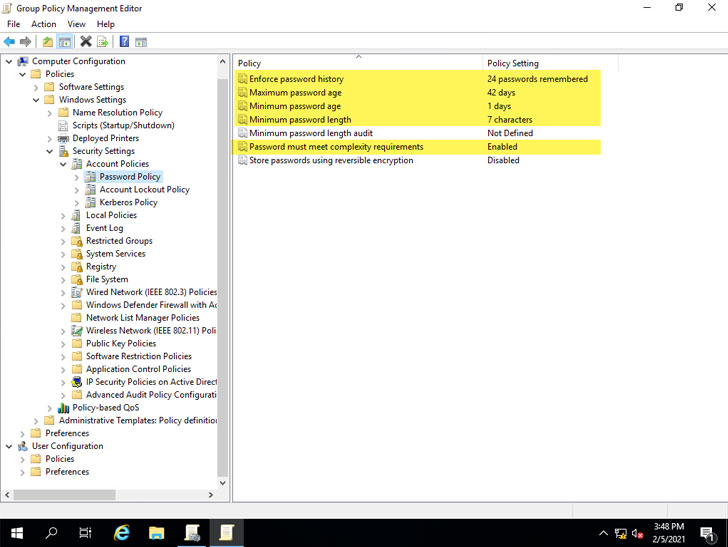 Default Windows Password Coverage options outlined in Default Area Team Policy
Default Windows Password Coverage options outlined in Default Area Team Policy
As you can see, particular plan options are configured for you by default. These incorporate:
- Implement password heritage – 24 passwords remembered
- Greatest password age – 42 days
- Bare minimum password age – 1 day
- Bare minimum password size – 7 people
- Password ought to fulfill complexity prerequisites – Enabled
- Shop passwords making use of reversible encryption – Disabled
How do these defaults hold up with the present-day recommendations from major cybersecurity authorities pertaining to password tips?
Are Windows default password policy settings insecure?
There have been changes and powerful suggestions manufactured in current many years pertaining to password security that represent a change in password security suggestions. Business cybersecurity industry experts are emphasizing the need to have to verify passwords in opposition to acknowledged weak password lists (dictionaries) and are positioning significantly less emphasis on password expiration procedures that have extensive been a aspect of organization password insurance policies.
The National Institute of Criteria and Technology (NIST) produced the NIST Exclusive Publication 800-63B (Electronic Identity Tips – Authentication and Lifecycle Management).
In Segment 5.1.1, ‘Memorized Secrets,’ they notice this distinct guidance in regards to evaluating passwords with recognized passwords from a dictionary or breach list:
“When processing requests to build and change memorized techniques, verifiers SHALL assess the future techniques against a record that consists of values regarded to be commonly-made use of, expected, or compromised. For case in point, the checklist Might consist of, but is not constrained to:
- Passwords acquired from former breach corpuses.
- Dictionary phrases.
- Repetitive or sequential characters (e.g. ‘aaaaaa’, ‘1234abcd’).
- Context-particular phrases, this sort of as the name of the assistance, the username, and derivatives
- thereof.”
A different section of the NIST guidance to be aware with regards to obligatory password improvements on periodic intervals:
“Verifiers Should really NOT demand memorized secrets to be changed arbitrarily (e.g., periodically). Even so, verifiers SHALL power a improve if there is evidence of compromise of the authenticator.”
The NIST guidance in regards to periodic password modifications is now passively suggested by Microsoft. In the Security baseline (DRAFT) for Windows 10 v1903 and Windows Server v1903, Microsoft notes the subsequent regarding enforced periodic password improvements:
“Latest scientific exploration calls into question the benefit of several extended-standing password-security practices this kind of as password expiration procedures, and details alternatively to better alternate options these as implementing banned-password lists (a good example staying Azure Ad password safety) and multi-factor authentication. Though we advise these options, they are not able to be expressed or enforced with our advisable security configuration baselines, which are built on Windows’ built-in Team Policy options and can not include client-precise values.”
Microsoft’s steerage aids to position out a flaw with the built-in Active Listing Team Coverage capabilities. There are no designed-in usually means to enforce banned-passwords conveniently. Even though Microsoft does doc the procedure to sign up a password filter .dll in its guide right here, companies ought to generate their individual custom password filter .dlls. This procedure can entail its possess set of challenges.
Hunting at the other Team Plan Password Coverage defaults enabled, the 7-character minimal password duration falls quick of what is famous by quite a few leading cybersecurity ideal tactics and tips from foremost authorities.
Note down below the precise password coverage normal minimal password duration and if they advocate evaluating passwords with a dictionary list.
- SANS Institute (admins) – 12 characters, dictionary
- NIST – 8 figures, dictionary
- NCSC – dictionary
- Microsoft Technet – 14 people
- Microsoft Exploration – 8 people, dictionary
How can corporations quickly audit their present-day password insurance policies in their atmosphere and guarantee these fulfill the proposed password security very best procedures? How can banned password lists be simply executed in Lively Directory environments without the need of this constructed-in capability?
Specops Password Auditor and Password Plan
Both of those the Specops Password Auditor (No cost) and Specops Password Plan from Specops Computer software supply very sturdy instruments that can help corporations audit their recent password guidelines and immediately put into practice breached password defense and customized dictionaries.
Companies can carry out this operation devoid of the require to program and produce a custom password filter .dll.
Specops Password Auditor supplies an easy way to obtain visibility to password security pitfalls in your ecosystem swiftly. Notably, this features accounts with blank passwords, passwords set not to expire, breached passwords, stale admin accounts, and several other individuals. 1 of the functions it offers is the capacity to audit your password policies.
Under, the Specops Password Auditor will allow you to swiftly and simply audit your existing area password insurance policies and look at them versus top sector-conventional password plan recommendations.
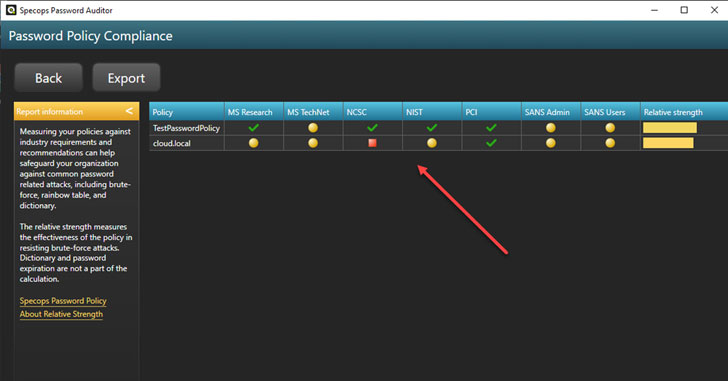 Comparing Energetic Listing Area Coverage with business most effective observe tips for passwords
Comparing Energetic Listing Area Coverage with business most effective observe tips for passwords
You can drill into each recommendation and see which unique requirement is not met by your existing Energetic Listing password policy.
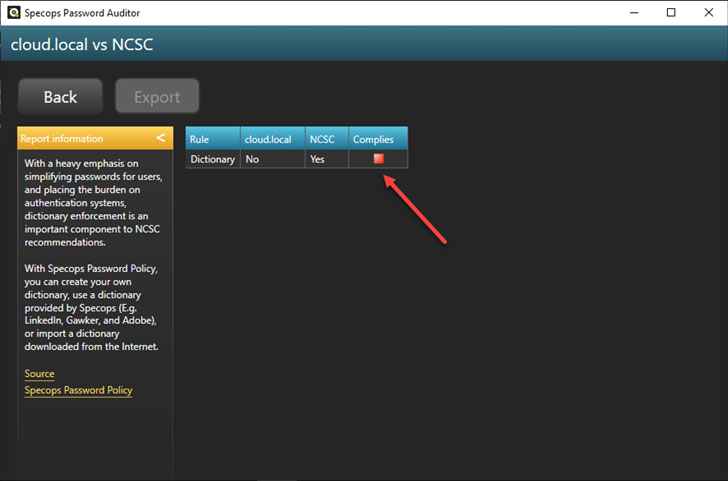 Viewing password coverage configurations in contrast to particular marketplace ideal tactics
Viewing password coverage configurations in contrast to particular marketplace ideal tactics
In addition to the visibility and attributes delivered by Specops Password Auditor, Specops Password Policy presents an effortless way to put into action banned-password lists in your Active Listing ecosystem. It also takes this a stage additional by permitting you to employ breached password defense.
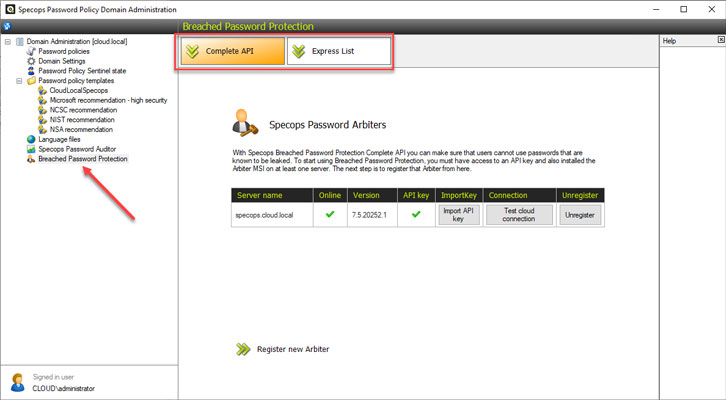 Specops Password Policy breached password safety
Specops Password Policy breached password safety
You can also drive people to alter passwords if their password becomes breached.
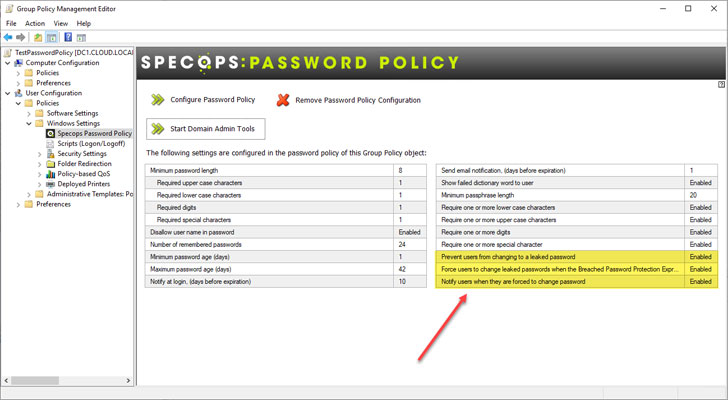 Power a password modify if an stop-person password turns into breached
Power a password modify if an stop-person password turns into breached
The breached and banned-password checklist functionality delivered by Specops Password Policy extends the Windows default password coverage. That’s why, businesses have a significantly far more sturdy and secure password plan for their ecosystem.
Wrapping Up
Password security is critical for the successful total security of your company-critical knowledge. Hackers are generally utilizing credential theft as an simple way into your IT infrastructure.
Microsoft Lively Directory Domain Companies (Adds) is a widely employed solution in most enterprise environments for identity and access management. It also handles the enforcement of password coverage for quite a few.
The Windows default password plan as configured and enforced by Lively Directory falls shorter in quite a few locations. Notably, it lacks any constructed-in capability to check passwords versus custom dictionary lists or breached password lists.
Specops Password Auditor and Password Policy assists companies swiftly obtain visibility to password risks in the environment and easily add banned-passwords and breached password listing defense.
Obtain Specops Password Auditor.
Identified this post interesting? Abide by THN on Facebook, Twitter and LinkedIn to go through additional unique content we put up.
Some components of this short article are sourced from:
thehackernews.com

 F5, CISA Warn of Critical BIG-IP and BIG-IQ RCE Bugs
F5, CISA Warn of Critical BIG-IP and BIG-IQ RCE Bugs