The U.S. Cybersecurity and Infrastructure Security Agency (CISA) and the Federal Bureau of Investigation (FBI) on Wednesday issued a joint advisory warning of lively exploitation of vulnerabilities in Microsoft Exchange on-premises merchandise by nation-point out actors and cybercriminals.
“CISA and FBI evaluate that adversaries could exploit these vulnerabilities to compromise networks, steal info, encrypt data for ransom, or even execute a harmful attack,” the businesses stated. “Adversaries may also offer access to compromised networks on the dark web.”
The attacks have mostly focused regional governments, educational institutions, non-governmental corporations, and business entities in several industry sectors, which include agriculture, biotechnology, aerospace, protection, lawful services, ability utilities, and pharmaceutical, which the businesses say are in line with past exercise carried out by Chinese cyber actors.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Tens of hundreds of entities, including the European Banking Authority and the Norwegian Parliament, are believed to have been breached to put in a web-based backdoor identified as the China Chopper web shell that grants the attackers the potential to plunder email inboxes and remotely entry the concentrate on devices.
The progress comes in light of the fast expansion of attacks aimed at vulnerable Exchange Servers, with several threat actors exploiting the vulnerabilities as early as February 27 right before they ended up eventually patched by Microsoft previous 7 days, swiftly turning what was labeled as “restricted and qualified” into an indiscriminate mass exploitation campaign.
When there is no concrete clarification for the common exploitation by so quite a few distinctive groups, speculations are that the adversaries shared or offered exploit code, resulting in other groups staying in a position to abuse these vulnerabilities, or that the teams attained the exploit from a prevalent vendor.
From RCE to Web Shells to Implants
On March 2, 2021, Volexity publicly disclosed the detection of numerous zero-day exploits applied to focus on flaws in on-premises variations of Microsoft Trade Servers, even though pegging the earliest in-the-wild exploitation exercise on January 3, 2021.

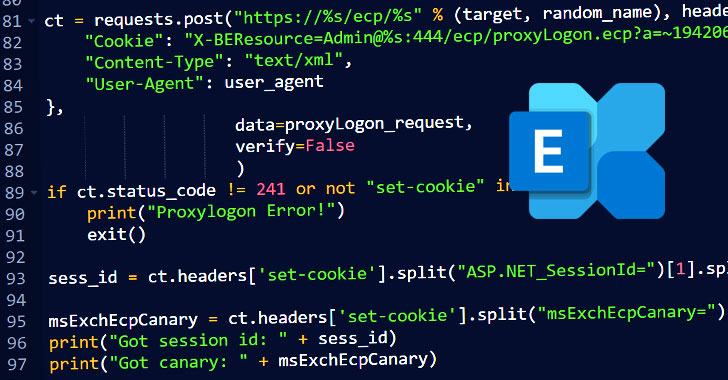
Thriving weaponization of these flaws, named ProxyLogon, lets an attacker to accessibility victims’ Trade Servers, enabling them to acquire persistent technique accessibility and handle of an enterprise network.
Though Microsoft in the beginning pinned the intrusions on Hafnium, a menace group that’s assessed to be point out-sponsored and running out of China, Slovakian cybersecurity agency ESET on Wednesday claimed it identified no much less than 10 diverse menace actors that very likely took advantage of the distant code execution flaws to set up destructive implants on victims’ email servers.
Apart from Hafnium, the 5 groups detected as exploiting the vulnerabilities prior to the patch launch are Tick, LuckyMouse, Calypso, Websiic, and Winnti (aka APT41 or Barium), with five other people (Tonto Team, ShadowPad, “Opera” Cobalt Strike, Mikroceen, and DLTMiner) scanning and compromising Exchange servers in the days right away next the launch of the fixes.
Even with no conclusive proof connecting the marketing campaign to China, Domain Tools’ Senior Security Researcher Joe Slowik famous that various of the aforementioned groups have been previously connected to China-sponsored exercise, which include Tick, LuckyMouse, Calypso, Tonto Staff, Mikroceen APT Group, and the Winnti Team.
“It appears clear that there are many clusters of groups leveraging these vulnerabilities, the teams are applying mass scanning or companies that enable them to independently target the exact units, and ultimately there are multiple versions of the code staying dropped, which may perhaps be indicative of iterations to the attack,” Palo Alto Networks’ Device 42 danger intelligence workforce mentioned.
In a person cluster tracked as “Sapphire Pigeon” by researchers from U.S.-based Purple Canary, attackers dropped a number of web shells on some victims at distinct situations, some of which have been deployed times in advance of they conducted follow-on exercise.
In accordance to ESET’s telemetry investigation, far more than 5,000 email servers belonging to organizations and governments from above 115 international locations are stated to have been impacted by malicious action linked to the incident. For its portion, the Dutch Institute for Vulnerability Disclosure (DIVD) reported Tuesday that it found 46,000 servers out of 260,000 globally that have been unpatched from the seriously exploited ProxyLogon vulnerabilities.
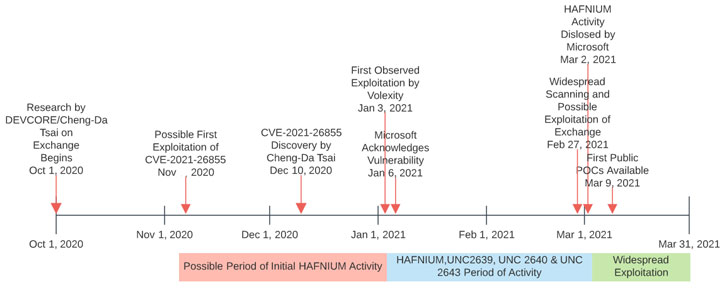
Troublingly, evidence factors to the simple fact that the deployment of the web shells ramped up adhering to the availability of the patch on March 2, boosting the risk that extra entities have opportunistically jumped in to develop exploits by reverse engineering Microsoft updates as part of several, independent strategies.
“The working day after the launch of the patches, we begun to notice lots of more threat actors scanning and compromising Trade servers en masse,” mentioned ESET researcher Matthieu Faou. “Apparently, all of them are APT groups targeted on espionage, apart from one particular outlier that seems linked to a recognised coin-mining marketing campaign (DLTminer). It is nonetheless unclear how the distribution of the exploit transpired, but it is inescapable that much more and additional menace actors, which include ransomware operators, will have entry to it sooner or afterwards.”
Aside from installing the web shell, other behaviors similar to or impressed by Hafnium exercise contain conducting reconnaissance in target environments by deploying batch scripts that automate various features these types of as account enumeration, credential-harvesting, and network discovery.
General public Evidence-of-Strategy Offered
Complicating the problem further is the availability of what seems to be the first useful general public proof-of-concept (PoC) exploit for the ProxyLogon flaws in spite of Microsoft’s tries to get down exploits revealed on GitHub above the past several days.

“I’ve verified there is a community PoC floating all over for the comprehensive RCE exploit chain,” security researcher Marcus Hutchins claimed. “It has a few bugs but with some fixes I was capable to get shell on my check box.”
Also accompanying the PoC’s release is a thorough specialized write-up by Praetorian scientists, who reverse-engineered CVE-2021-26855 to build a thoroughly performing end-to-end exploit by determining variations between the vulnerable and patched versions.
Even though the scientists deliberately made a decision to omit critical PoC parts, the growth has also lifted considerations that the technical data could further speed up the advancement of a working exploit, in change triggering even additional danger actors to launch their own attacks.
As the sprawling hack’s timeline slowly crystallizes, what is very clear is that the surge of breaches from Trade Server seems to have occurred in two phases, with Hafnium using the chain of vulnerabilities to stealthily attack targets in a limited manner, before other hackers commenced driving the frenzied scanning exercise commencing February 27.
Cybersecurity journalist Brian Krebs attributed this to the prospect that “various cybercriminal teams in some way discovered of Microsoft’s plans to ship fixes for the Exchange flaws a 7 days previously than they’d hoped.”
“The most effective advice to mitigate the vulnerabilities disclosed by Microsoft is to apply the relevant patches,” Slowik said. “Even so, presented the speed in which adversaries weaponized these vulnerabilities and the comprehensive interval of time pre-disclosure when these were being actively exploited, numerous corporations will very likely want to shift into response and remediation pursuits to counter present intrusions.”
Found this report attention-grabbing? Adhere to THN on Fb, Twitter and LinkedIn to go through more special articles we article.
Some elements of this write-up are sourced from:
thehackernews.com

 Fixing the Weakest Link — The Passwords — in Cybersecurity Today
Fixing the Weakest Link — The Passwords — in Cybersecurity Today