Shutterstock
Security researchers at Sophos have identified a novel workaround exploit for a patched Microsoft Office flaw that allowed remote code execution by means of a system in Microsoft Phrase information.
The now-patched critical vulnerability, tracked as CVE-2021-40444, associated exploiting the system in a Word document which downloaded a Microsoft Cupboard (Cab) archive and utilizing it to download a destructive payload.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
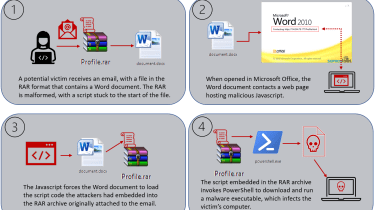
In the new an infection chain, attackers utilise the exact same bug in Microsoft Business office which will allow it to render browser internet pages in the context of an Office doc. In this scenario, a malicious Phrase file is put in in a malformed RAR archive loaded with a PowerShell script ahead of sending it as an attachment in spam e-mail.
The accompanying email invited recipients to uncompress the RAR archive to open the Phrase file opening the file would set off the front-conclusion script to run, foremost to an infection with Formbook malware.
The attack technique leverages the same bug which drove the patched RCE vulnerability but employs the identical system inside of Microsoft Business to retrieve a destructive payload with out making use of a Cab file.
Sophos
Formbook is an information and facts-harvesting malware strain that steals qualifications from browsers, in addition to collecting screenshots and logging keystrokes. The malware can also obtain and execute data files from a command and regulate server (C2) and has not long ago been observed in COVID-19-themed phishing campaigns, Check Position Investigate reported.
Researchers are contacting the new exploit a ‘CAB-less’ edition of the exact same flaw and consider attackers using it in the shorter 36-hour campaign they observed was evidence of a ‘dry run’ that could guide to even more incidents of exploitation.
“In idea, this attack strategy should not have labored, but it did,” stated Andrew Brandt, principal danger researcher at Sophos. “The pre-patch versions of the attack involved malicious code packaged into a Microsoft Cabinet file. When Microsoft’s patch closed that loophole, attackers uncovered a proof-of-idea that confirmed how you could bundle the malware into a different compressed file structure, a RAR archive.
“RAR archives have been used right before to distribute malicious code, but the procedure applied here was unusually challenging,” he added. “It probably succeeded only due to the fact the patch’s remit was very narrowly outlined and due to the fact the WinRAR software that people require to open up the RAR is very fault-tolerant and does not surface to brain if the archive is malformed, for instance, because it is been tampered with.”
Brandt also mentioned the discovery is proof of the point patching is not usually the only way to secure towards all cyber threats in all circumstances. In this style of attack, victims are lured into clicking an ‘enable content’ button inside the Word file which triggers the destructive script.
He said it is critical for organizations to teach staff on cyber risk administration and to normally check with experts inside the organisation if they are unsure about the legitimacy of any offered file or email.
Some areas of this posting are sourced from:
www.itpro.co.uk


 Tropic Trooper Cyber Espionage Hackers Targeting Transportation Sector
Tropic Trooper Cyber Espionage Hackers Targeting Transportation Sector