A hacking team connected to a Chinese-speaking danger actor has been joined to an state-of-the-art cyberespionage marketing campaign concentrating on authorities and armed service companies in Vietnam.
The attacks have been attributed with small assurance to the superior persistent danger (APT) named Cycldek (or Goblin Panda, Hellsing, APT 27, and Conimes), which is acknowledged for working with spear-phishing methods to compromise diplomatic targets in Southeast Asia, India, and the U.S. at the very least given that 2013.
In accordance to researchers from Kaspersky, the offensive, which was noticed in between June 2020 and January 2021, leverages a method called DLL facet-loading to execute shellcode that decrypts a final payload dubbed “FoundCore.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
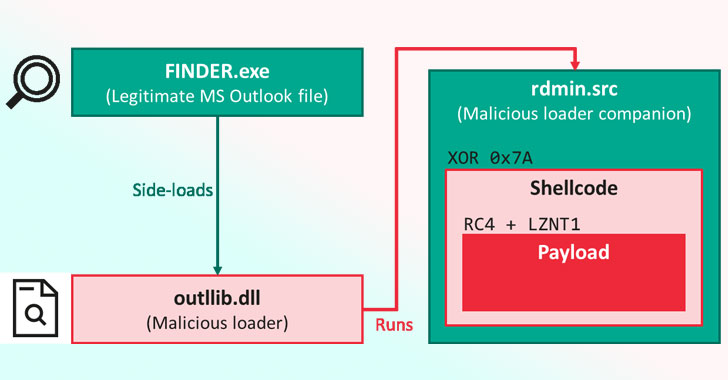
DLL aspect-loading has been a tried out-and-tested strategy used by various menace actors as an obfuscation tactic to bypass antivirus defenses. By loading destructive DLLs into legit executables, the concept is to mask their malicious activity less than a trusted technique or computer software procedure.
In this infection chain unveiled by Kaspersky, a reputable part from Microsoft Outlook hundreds a malicious library known as “outlib.dll,” which “hijacks the meant execution flow of the method to decode and operate a shellcode put in a binary file, rdmin.src.”
What is a lot more, the malware will come with an excess layer designed explicitly to safeguard the code from security assessment and make it hard to reverse-engineer. To attain this, the risk actor behind the malware is reported to have scrubbed most of the payload’s header, while leaving the rest with incoherent values.
Kaspersky claimed the system “alerts a important development in sophistication for attackers in this region.”
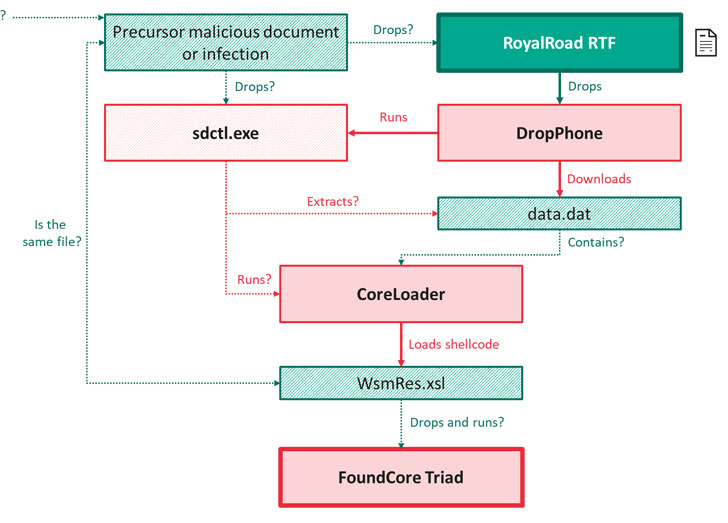
Other than providing the attackers whole manage above the compromised device, FoundCore comes with capabilities to operate commands for file system manipulation, course of action manipulation, capturing screenshots, and arbitrary command execution. Infections involving FoundCore had been also identified to down load two added malware. The first, DropPhone, gathers surroundings-related facts from the sufferer machine and exfiltrates it to DropBox, even though the 2nd, CoreLoader, runs code that enables the malware to thwart detection by security solutions.
The cybersecurity business theorized the attacks originate with a spear-phishing marketing campaign or other precursor bacterial infections, which result in the download of decoy RTF paperwork from a rogue web site, finally top to the deployment of FoundCore.
Between dozens of influenced businesses, 80% of them are dependent in Vietnam and belong to the government or military services sector, or are usually relevant to the health and fitness, diplomacy, training, or political verticals, with other victims, sometimes spotted in Central Asia and Thailand.
“No subject which team orchestrated this campaign, it constitutes a substantial move up in conditions of sophistication,” the researchers concluded. “Listed here, they’ve added quite a few a lot more layers of obfuscation and significantly complicated reverse engineering.”
“And this indicators that these teams could be on the lookout to extend their functions. Ideal now, it may well appear to be as if this marketing campaign is a lot more of a neighborhood danger, but it really is very probably the FoundCore backdoor will be uncovered in more international locations in distinctive locations in the upcoming,” stated Kaspersky senior security researcher Mark Lechtik.
Identified this short article exciting? Adhere to THN on Fb, Twitter and LinkedIn to read through extra exceptional written content we put up.
Some parts of this article are sourced from:
thehackernews.com

 Hackers Targeting professionals With ‘more_eggs’ Malware via LinkedIn Job Offers
Hackers Targeting professionals With ‘more_eggs’ Malware via LinkedIn Job Offers