Modern business networks are advanced environments with various sorts of wired and wi-fi equipment becoming connected and disconnected. The present gadget discovery solutions have been primarily targeted on pinpointing and monitoring servers, workstation PCs, laptops and infrastructure equipment these types of as network firewalls, switches and routers, because the most useful information and facts property of businesses are becoming saved, processed and transferred in excess of all those units, hence producing them the key concentrate on of security breaches and intrusions.
Nevertheless, a new trend has been rising in the earlier four a long time, the place attackers have been focusing on reason-constructed linked devices these as network printers and online video conferencing units as an entry level and information exfiltration route.
These units cannot be recognized effectively by the latest IT asset discovery methods for the following key causes:

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
- Proprietary protocols are typically used for managing and checking such products that are not known to the asset discovery remedy.
- Agent-centered asset discovery is not possible simply because most of the connected gadgets are resource-constrained programs with proprietary running systems that do not permit the installation of discovery agent application on them.
Firmalyzer’s IoT vulnerability assessment option (IoTVAS) overcomes these restrictions and offers:
- Precise identification of connected machine manufacturer, product title, gadget type, product conclusion of everyday living status, firmware edition, and firmware launch date
- Real-time Firmware bill of supplies (BOM) report that lists application factors and libraries within the firmware code of every single system with no requiring the person to add machine firmware files.
- Identification of publicly unknown vulnerabilities of the gadget that incorporates vulnerable 3rd party components, default credentials, crypto keys, certificates, and default configuration issues
- Identification of the publicly known vulnerabilities (CVEs) of the machine
IoTVAS can function as a standalone IoT discovery and risk evaluation solution or be built-in into current IT asset discovery, network port scanners, and IT vulnerability scanning resources via IoTVAS Relaxation API.
IoT Discovery with IoTVAS
IoTVAS identifies gadgets primarily based on fingerprints derived from machine network service banners. The gadget MAC deal with can also be utilized alongside one another with this fingerprint to strengthen detection precision, but it is not a need for IoTVAS, compared with the other unit discovery remedies. New unit fingerprints are repeatedly additional to the IoTVAS fingerprints database, dependent on the incoming API request and in-house investigate.
At the time of composing this report, this database is made up of above 50,000 fingerprints for additional than 2,300 machine brands. IoTVAS employs the following network provider response and banners for fingerprint generation:
- SysDescr OID string of the SNMP services
- SysObjectID OID string of the SNMP provider
- FTP support banner
- Telnet services banner
- Gadget hostname
- Uncooked reaction of the device webserver (http and HTTPS solutions)
- UPnP discovery response
- Optional MAC deal with of device network interface
IoTVAS would need at minimum a person of the earlier mentioned options for identifying an IoT machine. Network support banners can be collected by current network port scanners or IT vulnerability scanners.
In the standalone method, IoTVAS utilizes a light-weight network support identification software program that probes devices on the focus on network to extract the aforementioned attributes. IoTVAS gadget discovery capacity can also be integrated into the existing security tools by way of a Relaxation API endpoint.
IoT security Audit with IoTVAS
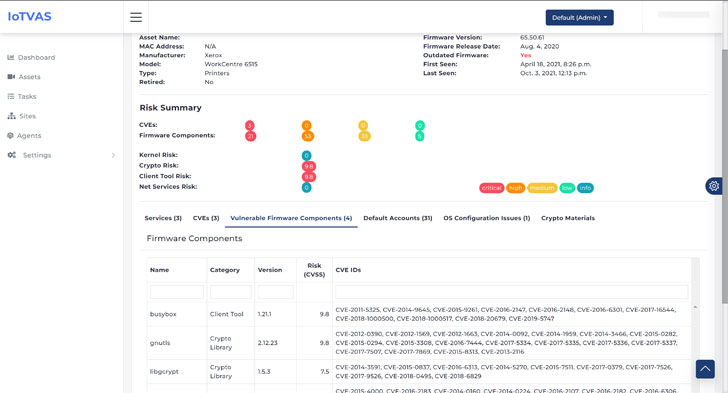
At the time a system maker, design and firmware variation ended up recognized, IoTVAS goes past just hunting up the CVEs affiliated with the product and firmware variation. Employing Firmalyzer’s proprietary firmware risk know-how base, IoTVAS retrieves firmware bill of resources and thorough risk examination that involves vulnerable 3rd party elements in the firmware in the pursuing categories: “network companies” (UPnP server, web server, etc.), “crypto libraries” (OpenSSL, GnuTLS, etc.), “Linux OS kernel” and “consumer applications” (busybox, and many others.).
IoTVAS also supplies a record of default credentials, crypto keys embedded in the machine firmware, lively and expired digital certificates, weak crypto keys and certificates, and default configuration issues. This in-depth data permits security professionals to proactively detect significant-risk related equipment in the network and initiate mitigation efforts just before these equipment get compromised. This also automates the method of BOM inventory of IoT and embedded equipment in the firm by removing the will need for handbook firmware down load and firmware binary investigation for many IoT equipment deployed in company networks.
Identical to the unit discovery capacity, IoTVAS firmware risk assessment is also obtainable by using a Relaxation API endpoint.
IoTVAS in Action
The adhering to determine exhibits the risk assessment report of a Xerox network printer in the IoTVAS SaaS edition, which includes the firmware BOM and vulnerability aspects of application components.
IoTVAS API enables IT security answer companies and SecOps groups to combine IoTVAS discovery and IoT risk audit capabilities into their current resources and choices. As an case in point, Firmalyzer produced IoTVAS plugin for the NMAP scanner that permits it to accurately discover and audit IoT products when scanning a target network.
The subsequent illustration exhibits how IoTVAS NSE scripts enable NMAP to properly detect the maker, product title, the firmware edition of an organization printer, alongside with its acknowledged CVEs and firmware threats. The firmware risk analysis reveals “root” and “postgres” default accounts and credentials for the “intFTP” account, a list of expired certificates and certificates with weak fingerprinting algorithm (MD5) and a default configuration of SSH daemon that will allow remote root login.
To get started out with IoTVAS API, you should sign-up for a demo API vital. The API documentation web site includes a swagger UI that lets you to evaluate IoTVAS endpoints suitable from your browser without composing any code
If you are fascinated in a demo of the IoTVAS SaaS or customization, really don’t hesitate to get in contact with Firmalyzer for a reside demonstration or a examination account.
Identified this short article attention-grabbing? Follow THN on Facebook, Twitter and LinkedIn to browse extra unique articles we publish.
Some parts of this post are sourced from:
thehackernews.com


 US indicts Indian call center scammers
US indicts Indian call center scammers