Microsoft on Thursday disclosed an “comprehensive collection of credential phishing strategies” that takes advantage of a tailor made phishing kit that stitched alongside one another factors from at minimum five unique broadly circulated types with the aim of siphoning person login information.
The tech giant’s Microsoft 365 Defender Threat Intelligence Staff, which detected the 1st instances of the tool in the wild in December 2020, dubbed the copy-and-paste attack infrastructure “TodayZoo.”


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“The abundance of phishing kits and other tools accessible for sale or hire will make it uncomplicated for a lone wolf attacker to select and pick out the very best capabilities from these kits,” the researchers explained. “They place these functionalities together in a tailored kit and consider to enjoy the positive aspects all to themselves. Such is the situation of TodayZoo.”
Phishing kits, often bought as just one time payments in underground forums, are packaged archive documents that contains photos, scripts, and HTML web pages that enable a risk actor to set up phishing e-mail and internet pages, using them as lures to harvest and transmit credentials to an attacker-controlled server.
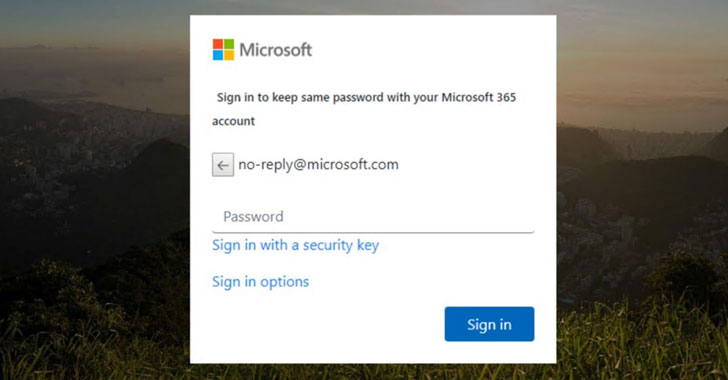
The TodayZoo phishing campaign is no unique in that the sender e-mail impersonate Microsoft, boasting to be password reset or fax and scanner notifications, to redirect victims to credential harvesting web pages. Where it stands out is the phishing package alone, which is cobbled collectively out of chunks of code taken from other kits — “some accessible for sale by publicly accessible scam sellers or are reused and repackaged by other package resellers.”
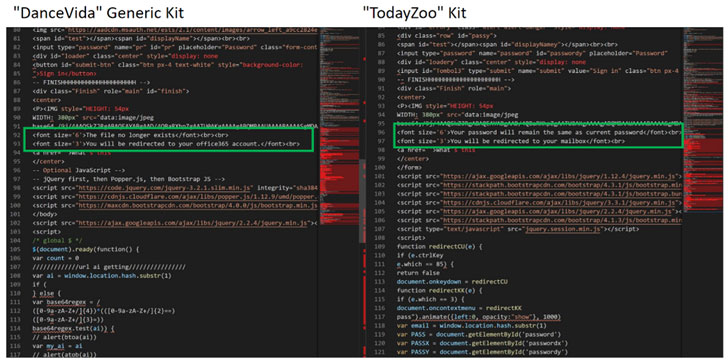
Precisely, massive areas of the framework seem to have been lifted generously from a further package, acknowledged as DanceVida, while imitation and obfuscation-related factors noticeably overlap with the code from at minimum five other phishing kits this sort of as Botssoft, FLCFood, Business office-RD117, WikiRed, and Zenfo. Inspite of relying on recycled modules, TodayZoo deviates from DanceVida in the credential harvesting element by replacing the primary features with its individual exfiltration logic.
If anything at all, the “‘Frankenstein’s monster attribute of TodayZoo” illustrates the varied approaches danger actors leverage phishing kits for nefarious reasons, regardless of whether be it by renting them from phishing-as-a-company (PhaaS) providers or by setting up their have variants from the floor up to accommodate their goals.
“This study even more proves that most phishing kits observed or available these days are primarily based on a more compact cluster of larger sized package ‘families,'” Microsoft’s evaluation study. “Whilst this craze has been noticed earlier, it proceeds to be the norm, provided how phishing kits we have viewed share massive quantities of code amid on their own.”
Found this posting attention-grabbing? Stick to THN on Facebook, Twitter and LinkedIn to study a lot more unique material we put up.
Some elements of this write-up are sourced from:
thehackernews.com

 Feds Reportedly Hacked REvil Ransomware Group and Forced it Offline
Feds Reportedly Hacked REvil Ransomware Group and Forced it Offline