Security researchers Thursday disclosed a new critical vulnerability impacting Area Title System (DNS) resolvers that could be exploited by adversaries to carry out denial-of-service attacks from authoritative nameservers.
The flaw, identified as ‘TsuNAME,’ was learned by researchers from SIDN Labs and InternetNZ, which manage the national top-stage internet domains ‘.nl’ and ‘.nz’ for the Netherlands and New Zealand, respectively.
“TsuNAME happens when area names are misconfigured with cyclic dependent DNS documents, and when vulnerable resolvers access these misconfigurations, they start off looping and mail DNS queries fast to authoritative servers and other resolvers,” the scientists said.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

A recursive DNS resolver is just one of the main factors included in DNS resolution, i.e., converting a hostname these kinds of as www.google.com into a personal computer-helpful IP deal with like 142.250.71.36. To realize this, it responds to a client’s ask for for a web webpage by producing a collection of requests until eventually it reaches the authoritative DNS nameserver for the asked for DNS document. The authoritative DNS server is akin to a dictionary that retains the actual IP address for the area which is becoming seemed up.
But with TsuNAME, the concept is that misconfigurations all through domain registration can develop a cyclic dependency these that nameserver information for two zones position to every single other, primary susceptible resolvers to “merely bounce back from zone to zone, sending non-end queries to the authoritative servers of both equally father or mother zones,” thus overpowering their mum or dad zone authoritative servers.
As to how this happens, it all boils down to recursive resolvers staying oblivious to the cycle and not caching cyclically dependent title documents.
Info gathered from the .nz domain identified that two misconfigured domains by yourself led to a 50% boost in over-all site visitors quantity for the .nz’s authoritative servers. Google Public DNS (GDNS) and Cisco OpenDNS — which ended up abused to focus on .nz and .nl domains in 2020 — have due to the fact resolved the issue in their DNS resolver computer software.
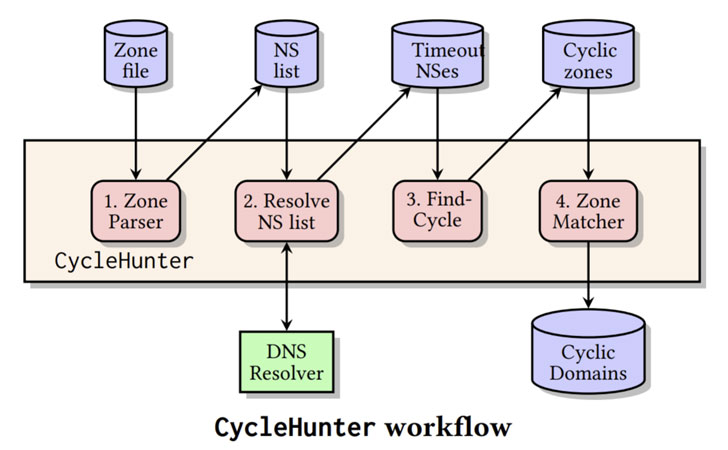
To mitigate the impression of TsuNAME in the wild, the researchers have posted an open-resource instrument named CycleHunter that allows for authoritative DNS server operators to detect cyclic dependencies. The examine also analyzed 184 million domains spanning 7 large leading-amount domains and 3.6 million distinctive nameserver documents, uncovering 44 cyclic dependencies utilized by 1,435 area names.
“Presented that [nameserver] information can improve at any time, there is no permanent option,” the researchers cautioned. “In other words and phrases, if a DNS zone has no cyclically dependent NS documents at time t, it indicates that this zone is not susceptible at only that specific time t. We therefore also recommend that registrars operate CycleHunter on a standard basis, for occasion, as aspect of their area name registration approach.”
Found this write-up interesting? Adhere to THN on Fb, Twitter and LinkedIn to read extra special content material we write-up.
Some sections of this report are sourced from:
thehackernews.com


 Millions of Households at Risk from Outdated Routers
Millions of Households at Risk from Outdated Routers