A new unpatched security vulnerability has been disclosed in the open up-source Horde Webmail client that could be exploited to attain remote code execution on the email server only by sending a specially crafted email to a victim.
“The moment the email is viewed, the attacker can silently take in excess of the finish mail server devoid of any more consumer conversation,” SonarSource claimed in a report shared with The Hacker Information. “The vulnerability exists in the default configuration and can be exploited with no understanding of a focused Horde instance.”
The issue, which has been assigned the CVE identifier CVE-2022-30287, was claimed to the vendor on February 2, 2022. The maintainers of the Horde Challenge did not instantly reply to a ask for for remark concerning the unresolved vulnerability.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

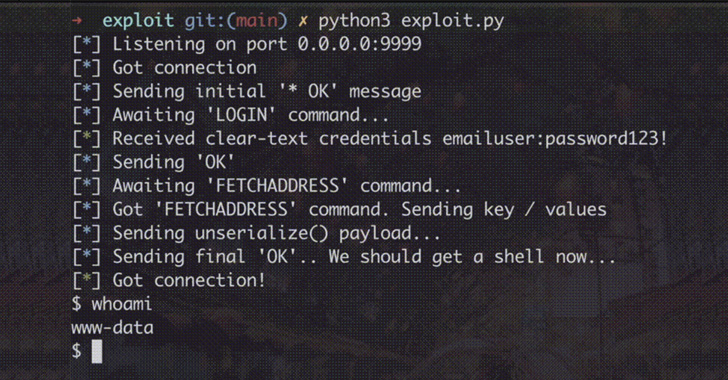
At its core, the issue can make it feasible for an authenticated consumer of a Horde occasion to operate destructive code on the fundamental server by getting edge of a quirk in how the customer handles call lists.
This can then be weaponized in relationship with a cross-web-site ask for forgery (CSRF) attack to trigger the code execution remotely.
CSRF, also referred to as session driving, happens when a web browser is tricked into executing a malicious motion in an software to which a user is logged in. It exploits the belief a web software has in an authenticated user.
“As a result, an attacker can craft a malicious email and incorporate an external graphic that when rendered exploits the CSRF vulnerability devoid of more conversation of a victim: the only prerequisite is to have a sufferer open up the malicious email.”
The disclosure comes a little more than 3 months after a different 9-calendar year-old bug in the software package arrived to gentle, which could allow an adversary to get finish access to email accounts by previewing an attachment. This issue has due to the fact been settled as of March 2, 2022.

In light-weight of the fact that Horde Webmail is no longer actively managed given that 2017 and dozens of security flaws have been documented in the productiveness suite, buyers are recommended to change to an alternate company.
“With so significantly have confidence in being put into webmail servers, they the natural way come to be a hugely
intriguing concentrate on for attackers,” the researchers reported.
“If a advanced adversary could compromise a webmail server, they can intercept each despatched and obtained email, obtain password-reset inbound links, delicate files, impersonate staff and steal all qualifications of end users logging into the webmail
service.”
Identified this posting appealing? Stick to THN on Facebook, Twitter and LinkedIn to study extra exclusive information we write-up.
Some parts of this write-up are sourced from:
thehackernews.com

 FluBot Android Spyware Taken Down by Global Law Enforcement Operation
FluBot Android Spyware Taken Down by Global Law Enforcement Operation