You don’t like possessing the FBI knocking on your door at 6 am in the morning. Remarkably, nor does your usual cybercriminal. That is why they conceal (at least the superior ones), for instance, guiding layers of proxies, VPNs, or TOR nodes.
Their IP handle will never ever be uncovered specifically to the target’s machine. Cybercriminals will constantly use 3rd-party IP addresses to supply their attacks.
There are innumerable methods to produce cyberattacks. But 1 thing is typical to all of them. The want for a pool of IP addresses to provide as a medium. Criminals want IP addresses to deliver distributed denial of support attacks.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Criminals need IP addresses to disguise guiding when probing providers. Criminals require IP addresses to attempt brute force attacks. Criminals will need IP addresses to run bot networks and expert services. In a nutshell, criminals need to have to sustain IP addresses beneath their management for rather considerably something. It is their most critical asset and is the ammo they need to supply attacks.
So how do cybercriminals get their hand on these infamous IP addresses, and what does this charge them? Here are some illustrations.
“admin/admin”
Hijacking devices and additional especially networks of IoT devices. Poorly secured and managed fleets of IoT gadgets left with default entry qualifications and out-of-date firmware are the best focus on for that. Simple way to zombify a big amount of devices, freshly served for DDoS attacks…hey “wise” security cameras…we are watching you!
“VPS are low-cost”
Acquire any cloud supplier, fire up some situations, set up bots to scan & try Log4j injections. At a confined charge, you have your bot network to scan targets for vulnerabilities. Of class, at some level, you will get flagged or the company may possibly catch you. But you can replicate your technique with cloud providers in other international locations, it’s possible much less about the use of these VPS…
‘Into darkness”
They can also go to the grocery store for criminals, aka. “dark web” and acquire a network of bots to supply attacks like DDoS for a few of hundred pounds. Script kiddies, welcome.
Two choose-aways from these techniques :
Acquiring IP addresses, whilst not difficult, fees income, time, and sources. Tamper with that, you tamper with a criminal’s means to do his work effectively. Ban known IPs utilised by criminals and you may just dramatically increase the security of your on-line belongings.
These bots and scan automation functions produce a lot of internet track record sound. Consider all individuals countless botnets scanning the IP space for diverse nefarious needs. This is perfectly acknowledged by SOC analysts as “warn tiredness”, indicating, this generates a large amount of money of information, devoid of significantly-extra price, but that analysts nevertheless need to have to just take into account.
But good news everyone, there are alternatives to make everyday living a lot more complicated for cybercriminals.
IP standing is portion of the answer. Suppose buyers can preventively assess the risk of an IP connecting to a services. In that circumstance, it can lock out acknowledged malicious people and make absolutely sure these IPs can not harm any person any more, de-facto having away the IP handle pool criminals spent time and money to establish.
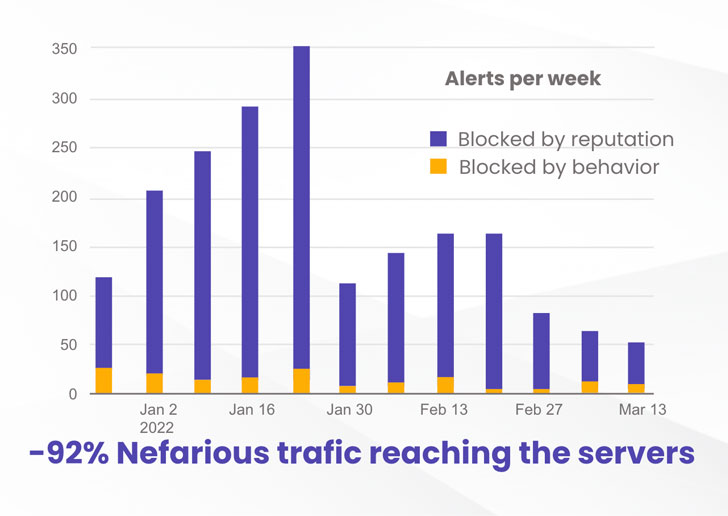
At CrowdSec, we did exciting experimenting: we established up two equivalent VPSs on a properly-known cloud provider, with two simple providers, SSH and Nginx. Nothing fancy, just like millions of machines out there in the wild. CrowdSec was put in on equally to detect intrusion attempts. Continue to, a single device experienced the remediation agent (IPS), receiving IP track record facts from the CrowdSec local community (each day 1 million signals shared) and preventively banning flagged IPs.
The end result was fairly stunning.
Many thanks to the community blocklist, the equipment with the IPS preventively blocked 92% of the attacks when compared to the equipment without the need of the IPS. That is a notable maximize in security level.
You can go through extra about the methodology and detailed benefits at: https://crowdsec.net/
 Resource: crowdsec.net
Resource: crowdsec.net
Neighborhood IP blocklists – with the earlier curation – just take care of both of those worries.
It cripples criminals by nullifying their IP tackle pool. They expended time, funds, resources to make them, and we, as a community, just get them absent in the blink of an eye. Choose that scum!
But it also would make the lifetime of analysts and cybersecurity gurus significantly simpler. By preventively blocking people nefarious IPs, the qualifications sounds is appreciably lessened. We are talking about reducing by 90% the alerts that need to be analyzed by SOC individuals. That is a great deal additional time to aim on far more significant alerts and subject areas. Alert exhaustion? – bye-bye.
If you would like to partake in the greatest IP status neighborhood and hunt nefarious IP addresses although effectively shielding your on the web belongings, be part of us at crowdsec.net
Identified this report interesting? Adhere to THN on Facebook, Twitter and LinkedIn to study a lot more special material we submit.
Some elements of this write-up are sourced from:
thehackernews.com


 Estonian Gets 66 Months for Ransomware Conspiracy
Estonian Gets 66 Months for Ransomware Conspiracy