I am positive you would concur that, in modern electronic globe, the bulk of purposes we perform on need some type of credentials – to hook up to a database with a username/password, to obtain pc systems by way of licensed tokens, or API keys to invoke expert services for authentication.
Credentials, or at times just referred to as ‘Secrets,’ are pieces of person or technique-degree confidential facts that should to be carefully shielded and available to legitimate end users only. We all know how vital it is to retain these belongings protected to stop account misuse and breaches.
A actuality examine: How generally do you make proactive attempts to shield these assets? Not often, I might say.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Amongst the worst mistakes a developer can make when it arrives to application security is to unintentionally commit private info publicly on the Internet. Surprisingly, secrets and credentials are accidentally leaked extra usually than you could possibly assume, and there are intelligent resources that scan general public repositories in look for of committed techniques.
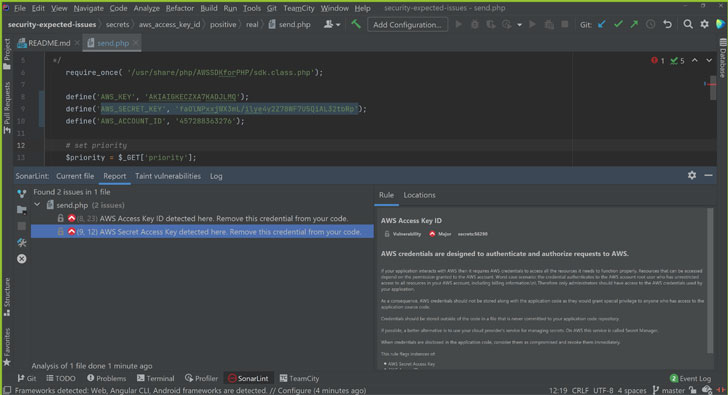
With the mission of empowering developers to acquire control of their very own code integrity, SonarLint, a totally free and open source IDE extension from SonarSource, not long ago announced a new aspect for its software that aims to assistance developers discover and avoid leaks of AWS user or program-level authentication credentials right before they are fully commited to a repository and leaked from user’s neighborhood resource code or data files.
Does this seem appealing to you? Proceed looking through to come across out much more.
Very first – why you ought to treatment
Let’s choose a instant to look again a minor and see why this new SonarLint aspect would be so significant and valuable to any developer.
Someplace in your existence, you might have utilised a credit card for on line purchase and immediately received a contact from the credit card company inquiring if you supposed to go forward with the buy. If you did, no trouble, all’s nicely. If not, fraudulent exercise was just caught prior to the transaction was total – preserving you and your credit rating card firm the complexity of an immediately after-the-simple fact compromised account.
The exact same applies to code growth.
There may well be a recurring relationship to a cloud-primarily based database as portion of the code enhancement and shipping and delivery system, or you might need to have credentials to obtain an API of a 3rd-party firm.
In that method, there is a possibility you really hard-coded credentials quickly to relieve use, or a colleague may well have included confidential info for a speedy local exam, and then unintentionally fully commited individuals data files to a public repository. And…those short term adjustments are now permanent….Yikes! Even with right after-the-truth deletion of the code, there is even now the chance that a person manufactured a duplicate of your solution in advance of the cleanup.
Up coming issue you know, anyone has compromised the account, or even worse nonetheless, this small security lapse has delivered another person with a tiny staging position for a larger infrastructure breach.
Breaches of this sort are extra frequent and potentially catastrophic than you may possibly recognize. There have been a selection of information articles or blog posts in the past yr highlighting incidents the place malicious consumers have stolen API keys embedded in community source code repositories these types of as GitHub and BitBucket. StackOverflow, Uber and a lot more not long ago Shopify are examples of substantial-profile security incidents where by secrets sprinkled in publicly noticeable data files designed havoc. Think about the damage it could have finished to the brand name status.
Human error will keep on to arise, but by undertaking the right checks at the appropriate time, the mistake can be prevented from developing in the 1st place. The previous circumstance illustrates how publicity of ‘secrets’ detected at the suitable level of introduction, e.g. through programming or just prior to committing your code, could have saved a good offer of issues.
The best location to detect and tackle these issues in your advancement workflow is at the quite starting of it, that is, in your IDE, Integrated development atmosphere. There are a ton of huge corporations that have acquired this lesson the tricky way.
Highly developed principles that detect AWS strategies in-IDE
With the latest addition of new regulations for detecting cloud tricks, SonarLint protects AWS authentication qualifications and Amazon Market Web Provider (MWS) credentials from leaking publicly. Verify out the regulations that safeguard MWS auth tokens, AWS Access Crucial, Vital ID, and Session tokens.
SonarLint protects your qualifications against public leakage by acting as your first line of defence. By flagging issues at the stage of introduction (i.e., shifting issue detection more still left), you can consider rapid motion and avert the leak in the first place.
This is crucial for the reason that compromised accounts can have not only individual or resource-stage ramifications, these as the chance of account hacking, but also adverse outcomes for the confidentiality of your prospects. For instance, compromised MWS tokens can be employed to get illicit accessibility to databases that include buyer information these as credit score card numbers, email, shipping and delivery addresses, and service provider revenue documents.
With SonarLint set up in your IDE, these ‘Secret’ detection procedures will permit you to capture the existence of these types of qualifications at the to start with stage of entry i.e., in the source code or in language-agnostic data files (e.g., xml, yaml, json) prior to they are dedicated to the repo.
Aside from determining these difficulties, SonarLint is also capable to supply clear direction on how to solve them. You then have comprehensive flexibility to consider motion and handle the code currently being flagged bringing you a single stage nearer to offering protected code.
Getting began in your IDE
This feature is presently supported in well-liked IDEs these as VS Code, IntelliJ Plan, PyCharm, CLion, WebStorm, PHPStorm, and Rider, with Visible Studio, Eclipse, and a lot more to adhere to.
To commence securing your code base you can down load SonarLint for VS Code or SonarLint for your JetBrains IDEs. Or if you were being already employing SonarLint in your IDE, you can simply just update the plugin to the latest variation to empower this feature.
As a future action, the organization also plans to increase the ‘Secrets’ detection features to other public cloud vendors. In the potential, you can assume SonarLint to support additional cloud companies, SaaS products, and database suppliers.
Developers who use other SonarSource alternatives – SonarQube or SonarCloud for delivering high-quality and secure code can extend their code security knowledge to their IDE. By setting up SonarLint for free of charge, not only can they instantly profit from impressive characteristics such as mystery detection but also make improvements to the overall code excellent and security of their code foundation by sharing policies and examination configurations from SonarQube or SonarCloud to SonarLint to coalesce the overall enhancement crew on a single definition of code health and fitness.
Discovered this posting intriguing? Abide by THN on Fb, Twitter and LinkedIn to read through far more unique material we publish.
Some areas of this article are sourced from:
thehackernews.com


 Researchers Uncover FIN8’s New Backdoor Targeting Financial Institutions
Researchers Uncover FIN8’s New Backdoor Targeting Financial Institutions