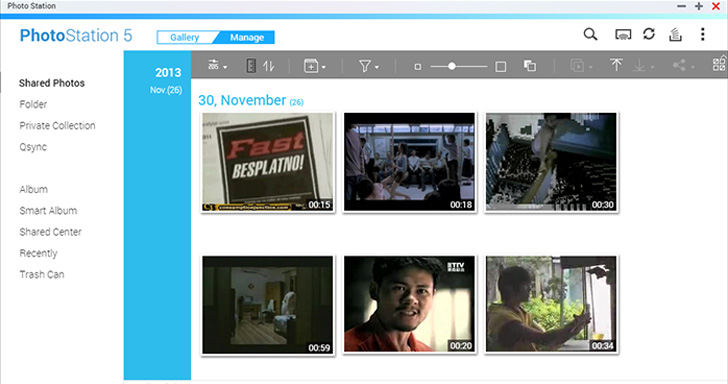
QNAP has issued a new advisory urging people of its network-connected storage (NAS) products to up grade to the latest model of Photograph Station next nonetheless an additional wave of DeadBolt ransomware attacks in the wild by exploiting a zero-working day flaw in the software package.
The Taiwanese business stated it detected the attacks on September 3 and that “the campaign seems to target QNAP NAS gadgets running Photo Station with internet publicity.”


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The issue has been resolved in the pursuing variations –
- QTS 5..1: Image Station 6.1.2 and later
- QTS 5../4.5.x: Image Station 6..22 and later on
- QTS 4.3.6: Photograph Station 5.7.18 and later
- QTS 4.3.3: Photo Station 5.4.15 and later
- QTS 4.2.6: Picture Station 5.2.14 and later
Information of the flaw remain unclear at the instant, with the company advising users to disable port forwarding on the routers, avoid NAS devices from getting obtainable on the Internet, upgrade NAS firmware, implement powerful passwords for user accounts, and get common backups to stop facts loss.

The newest improvement marks the fourth spherical of DeadBolt attacks aimed at QNAP appliances given that January 2022, followed by similar incursions in Might and June.
“QNAP NAS should really not be specifically related to the Internet,” the business stated. “We advocate end users to make use of the myQNAPcloud Website link function supplied by QNAP, or help the VPN service. This can correctly harden the NAS and minimize the opportunity of getting attacked.”
Located this short article intriguing? Adhere to THN on Fb, Twitter and LinkedIn to study additional exclusive articles we post.
Some parts of this article are sourced from:
thehackernews.com


 Keybank’s Customer Information Stolen By Hackers Via Third-party Provider
Keybank’s Customer Information Stolen By Hackers Via Third-party Provider