Securing apps it the API-initial period can be an uphill battle. As advancement accelerates, accountability gets unclear, and getting controls to function gets to be a challenge in alone. It is time that we rethink our software security tactics to reflect new priorities, rules and procedures in the API-very first era. Securing tomorrow’s purposes begins with examining the business enterprise hazards currently.
The tendencies and risks shaping present-day apps
As the entire world carries on to turn into far more and more interconnected by means of products — and the APIs that connect them — men and women are rising accustomed to the frictionless expertise that they offer. Even though this frictionless actuality is doubtlessly extra person-friendly, i.e., speedier and far more handy, it also demands a trade-off. This advantage requires openness, and openness is a risk when it comes to cybersecurity.
According to Sidney Gottesman, Mastercard’s SVP for Security Innovation, the over scenario qualified prospects to one particular of the most important trends shaping the security posture for present day applications: A crisis of have confidence in among persons and the apps they use.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
A second main pattern is that of the provide chain. Simply just handling your individual hazards is just not ample, as attacks more and more penetrate internal units via 3rd party, vendor-equipped elements. In electronic products and solutions and even connected hardware goods, provide chains are now composed of distinctive providers bundled jointly in the closing product as a result of APIs, generating a new style of integration risk rooted in the provide chain.

If the new Colonial Pipeline and JBS attacks suggest nearly anything, it can be that another important pattern is the abundance of destructive actors, equally at the particular person and state level. Businesses need to now think that quicker, somewhat than later on, they will be attacked and will have to be organized.
Abundance of facts can not be overlooked. Enterprises are storing, managing, and enabling obtain to so a lot info, generating the software layer (and APIs) extra appealing to attackers. Increasing regulations aimed at increasing the security postures of both public and private enterprises also get a special place in the landscape of security trends.
Application security isn’t what it employed to be
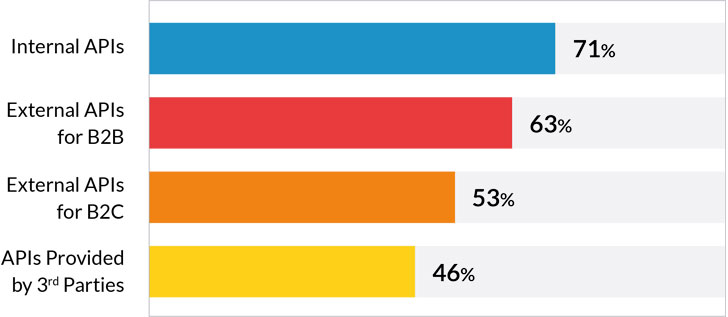
80% of enterprises now allow exterior entry to info and operation by way of APIs, in accordance to a modern marketplace study revealed by Imvision, on the lookout into the recent condition of API use and adoption amongst major enterprises. The outcomes are in line with other analysis on the matter and conclude that enterprises are a great deal much more open up than they made use of to be just a several a long time back – and escalating.
But this usually means that application security has moved over and above its “doorman” position of asking “who’s authorized in?” Today, software security ought to assume that consumers are now inside of the software and target on inquiring, “what do we let them to do?”, “what is actually the predicted usage?” and “how do we prevent undesirable habits?”.
According to Rob Cuddy, the World wide Software Security Evangelist at HCL, the fundamental shift enterprises will have to make in their tactic to software security is that securing the software perimeter from exterior penetration just isn’t going to make sense in the era of APIs.
Constructing levels of security close to the application will never get the job done when the application is exposed by means of APIs. Alternatively, a new within-out method is needed. This new method assumes application penetration in services of the user, but puts protective mechanisms in location in scenario that the actor is malicious.
Learn much more on how security gurus are rethinking software security
If you talk to builders, they’d tell you that security was there all alongside, but now it really is turn into critical. However, it truly is not an issue of incorporating new instruments or automations, but relatively a make a difference of earning a fundamental change in persons, procedures, and society.
In the race for superfast agile deliveries, a lot of enterprises are adopting a DevSecOps approach that mandates the integration of security practices inside the enhancement lifecycle. But although numerous are chatting about undertaking it, only about half are truly performing anything about it – this means, essentially possessing a total lifecycle API security in position.
Handling security among the disparate groups is no simple process
At Allegiant Airways, Main Facts Security Officer Rob Hornbuckle is leading an exciting initiative to enhance consciousness, visibility, and collaboration throughout teams and the growth lifecycle.
To create and preserve their client-dealing with apps, they have 10 persistent enhancement groups at any provided time. Nevertheless, orchestrating security among disparate teams is no wander in the park. It involves considerable visibility and a society change that encourages initiative and accountability-taking.
To hold security at the forefront, they established a security winner method that places two people on each individual crew with the responsibility for ensuring specific security standards throughout progress. These champions support the relaxation of the crew drive know-how and communication all through the entire technique.
This software empowers visibility into application security at the organizational amount through month-to-month conferences that concentration on almost everything that is happening with security inside of the unique application programming teams. These meetings enable the firm to supply metrics pertaining to the over-all security well being obtained by various teams time beyond regulation to assist attain buy-in from senior executives and board customers.
Visibility, or: “Being capable to identify what desires to be set first”
With numerous enterprises applying dozens, if not hundreds or additional, diverse security applications addressing various programs, CISOs are challenged to recognize what is of critical significance, so they can efficiently prioritize vulnerabilities to mitigate risk.
But just because a server is unpatched doesn’t automatically signify that it poses a correct business enterprise risk. What is actually required is not only visibility into vulnerabilities, but somewhat into the exposure it generates and the opportunity company impression in case of a breach.
To really be able to affiliate the organization risk with a vulnerability, Rob Hornbuckle believes that executive management demands the two a reliable comprehension of software programming, as nicely as formidable awareness of the inner workings of an organization’s organization model. This permits them to prioritize mitigation in accordance with the correct business effects of a opportunity breach on their unique business model.
Even if a distinct vulnerability was ready to disrupt functions at Colonial Pipeline, for case in point, it would not indicate that that exact same vulnerability holds any risk to a further organization’s base line, particularly if their enterprise model is distinct. The most important belongings to safeguard are these products and services and apps that expose critical business features.
Creating a see of software challenges within just the context of company risk management
Rallying the corporation about security is no effortless endeavor, especially when their input – as valuable and important as may perhaps be – usually generates delays and adds operate to harried enhancement teams. Making sure that all degrees of the group realize the value of the security group is a critical stage in implementing safe development processes.
At BNP Paribas, the World Head of Technology Risk Intelligence Sandip Wadje factors out that making it simple for the corporation to fully grasp just how massive their interior and external attack surfaces are and accurately which critical company functions are exposed, is paramount.
The first move is discovery – knowing what you have, how it can be utilized, why it exists. Though this move is really uncomplicated, in the 2nd move, governance, enterprises should really look for to recognize which methods they’re getting in conditions of application advancement, maintenance and ongoing monitoring. Organizations must assure that they have both a centralized governance committee or a 3rd party technology risk group to oversee interior group security steps.
The third phase is that of assurance relating to ongoing security measures. Ongoing security checking that repeatedly analyzes new vulnerabilities as they’re discovered drastically lessens risks, as exploited vulnerabilities are often all those that weren’t identified to the group.
Last but not least, resilience is yet another important functionality to establish. Putting in put concrete strategies for incident reaction and minimizing publicity is important in the situation that vulnerabilities have been exploited. As quite a few companies are by now making use of distinctive security methods, guaranteeing efficient use of these solutions in defending critical business apps is crucial.
Master a lot more on how to make your security workforce a necessity in the API-initially period.
Choose this example: at BNP Paribas, the security staff designed a blueprint of distinctive applications to have an understanding of how each and every one was impacted by the changeover to the cloud. This blueprint is employed by government administration to empower a check out of the unique workloads that could be securely migrated to the cloud.
They then made governance all over it, both equally at the corporate team amount, which targeted on strategy, and at the operational degree, which targeted on ongoing monitoring assurance. Their following phase was to create an API steering committee to prioritize providers in terms of their means to monetize information. Last but not least, they established up a 3rd party risk management system and involved significant interior stakeholders to produce their application security strategy.
The stunning upside of security laws
Much like people, groups also have a name. For security teams, it is hugely crucial to guarantee that in excess of time they usually are not viewed as a nuisance receiving in the way of speedy deliveries but rather as a enterprise enabler. This is the place regulations can in fact go a extended way in making sure that this isn’t really the situation.
By conditioning the start of new initiatives on adherence to security, protection, and compliance measures, security teams turn into a necessity. At the time security groups clearly attract lines involving laws, the vulnerabilities they explore, and the business effects, enhancement teams will stop seeing them as a nuisance.

This elevates security to a strategic organization enabler and even a aggressive differentiator.
At Mastercard, for instance, under the management of a CEO that has been concentrated on security from the get go, their company security workforce is at the heart of their business design and supplies security solutions to all of their shoppers and to the ecosystem at large.
Summary
In the API-era, corporations have to rethink their security posture. Trends like the crisis of self-confidence, source chain interconnectedness, laws, and the raising quantity of malicious actors dictate the change to an inside of-out strategy in terms of cybersecurity.
With more and more enterprises permitting customers to access information and features through APIs, the security point of view will have to transform from proscribing access to much better controls and permissions.
To get started, corporations need to very first ensure crystal clear visibility of vulnerabilities and the capability to prioritize according to company influence. Making certain that the complete organization understands the threats and challenges posed to their critical organization processes is also important.
Setting up official procedures, together with discovery, assurance, ongoing checking, and resilience, and lastly, changing the look at of security teams from a nuisance to a necessity is critical to delivery secure products and solutions.
*** This article is primarily based on the 1st session of the executive education and learning software by Imvision.
Identified this post intriguing? Adhere to THN on Facebook, Twitter and LinkedIn to go through far more exclusive information we publish.
Some sections of this short article are sourced from:
thehackernews.com


 Facebook Sues 4 Vietnamese for Hacking Accounts and $36 Million Ad Fraud
Facebook Sues 4 Vietnamese for Hacking Accounts and $36 Million Ad Fraud