Well known prompt messaging application WhatsApp on Thursday announced a new account verification characteristic that makes certain that malware functioning on a user’s cellular system will not affect their account.
“Cell unit malware is just one of the greatest threats to people’s privacy and security now due to the fact it can consider advantage of your phone devoid of your permission and use your WhatsApp to mail undesired messages,” the Meta-owned firm reported in an announcement.
Named Product Verification, the security evaluate is designed to help protect against account takeover (ATO) attacks by blocking the threat actor’s link and making it possible for the focus on to use the app without having any interruption.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
In other terms, the purpose is to deter attackers’ use of malware to steal authentication keys and hijack target accounts, and subsequently impersonate them to distribute spam and phishing inbound links.
This, in turn, is realized by introducing a security-token which is saved locally on the unit, a cryptographic nonce to discover if a WhatsApp consumer is speaking to the server to retrieve incoming messages, and an authentication-obstacle that acts as an “invisible ping” from the server to a user’s unit.
The client is essential to send the security-token each individual time it connects to the server. The security-token, for its part, is up to date each individual time it fetches an offline message from the server.
An authentication-problem is thought of a failure when the consumer responds to the obstacle from a distinct machine, indicating an anomalous link originating from an attacker. This triggers the link to be blocked.
Should really there be no response from the shopper, the method is retried a “several a lot more occasions,” soon after which the connection will be blocked if the customer nonetheless does not react.
WhatsApp reported Gadget Verification has been rolled out to all Android end users and that it is really in the procedure of being rolled out to iOS people.
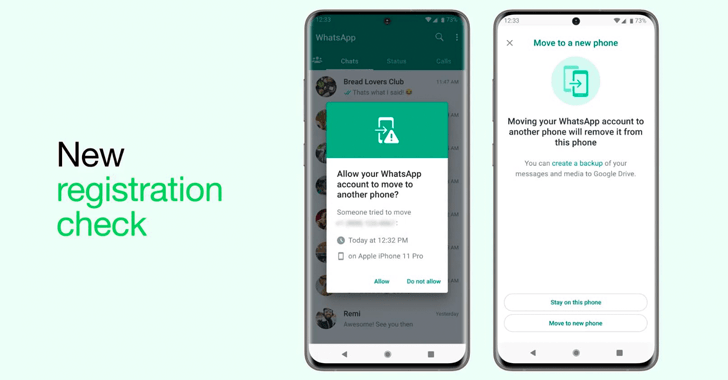
The function is aspect of a broader established of new enhancements that are built to authenticate and validate users’ identities, together with displaying alerts when there is an try to migrate a WhatsApp account from a single system to an additional.
Also introduced by WhatsApp is a “Vital Transparency” feature to immediately verify whether or not chats are end-to-finish encrypted without the need of necessitating any further steps from the user.
To do so, it truly is implementing a new Auditable Essential Directory (AKD) that’s based mostly on current protocols like CONIKS and SEEMless to enable buyers verify their discussion security.
“The AKD will enable WhatsApp consumers to instantly validate that a user’s encryption crucial is authentic and allows everyone to validate audit-proofs of the directory’s correctness,” the company explained.
Forthcoming WEBINARMaster the Artwork of Dark Web Intelligence Gathering
Master the art of extracting menace intelligence from the dark web – Join this skilled-led webinar!
Save My Seat!
Verification presently demands buyers in a chat to manually compare the security code (which exists as a QR code and a 60-digit number) by sending it to the participant on the other conclusion by using SMS or email, or alternatively by scanning the QR code if the functions are physically next to each and every other.
The security code is nothing but a exceptional hash of both equally the public/non-public critical pair which is generated to facilitate finish-to-end encrypted messaging. It can transform when people change gadgets or reinstall WhatsApp.
Critical Transparency streamlines the verification course of action by making use of an automatic move that maintains a report of public vital alterations in a directory, thereby enabling a consumer to look at towards it.
WhatsApp intends to make this characteristic are living in the coming months, though it really is currently hosting and working an Auditable Essential Directory of all its buyers. “This is an vital system that empowers security-acutely aware customers to validate an finish-to-finish encrypted personalized conversation immediately,” the business included.
Located this short article attention-grabbing? Stick to us on Twitter and LinkedIn to go through more unique written content we post.
Some parts of this report are sourced from:
thehackernews.com

 New Python-Based “Legion” Hacking Tool Emerges on Telegram
New Python-Based “Legion” Hacking Tool Emerges on Telegram