Four separate security bugs would give attackers practically complete command and persistence around qualified devices, many thanks to a defective update mechanism.
A significant-severity series of four vulnerabilities can let distant adversaries to obtain arbitrary code execution in the pre-boot surroundings on Dell gadgets, scientists mentioned. They affect an approximated 30 million person Dell endpoints all over the world.
According to an evaluation from Eclypsium, the bugs impact 129 unique models of laptops, tablet and desktops, including enterprise and shopper units, that are shielded by Safe Boot. Safe Boot is a security typical aimed at making absolutely sure that a product boots applying only software package that is reliable by the system authentic devices producer (OEM), to protect against rogue takeovers.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The bugs let privileged network adversaries to circumvent Safe Boot protections, regulate the device’s boot course of action and subvert the running method and better-layer security controls, scientists at Eclypsium said on Thursday. They carry a cumulative CVSS rating of 8.3 out of 10.
Exclusively, the issues influence the BIOSConnect function in just Dell SupportAssist (a technological assistance solution that will come preinstalled on most Windows-centered Dell devices). BIOSConnect is used to conduct distant OS recoveries or to update the firmware on the product.
“Technology vendors of all kinds are increasingly utilizing around-the-air update processes to make it as uncomplicated as doable for their shoppers to maintain their firmware up to day and get better from technique failures,” researchers pointed out, in an investigation. “And whilst this is a beneficial possibility, any vulnerabilities in these procedures, this kind of as all those we’ve viewed here in Dell’s BIOSConnect, can have serious repercussions.”
The report famous that the particular vulnerabilities make it possible for an attacker to remotely exploit the UEFI firmware of a host and obtain control above the most privileged code on the gadget.
“This mix of remote exploitability and significant privileges will probable make distant update features an alluring goal for attackers in the long term,” the report concluded.
Insecure TLS Relationship: Impersonating Dell
The initially vulnerability (CVE-2021-21571) is the beginning of a chain that can guide to remote code execution (RCE).
When BIOSConnect attempts to hook up to the backend Dell HTTP server to accomplish a remote update or recovery, it permits the system’s BIOS (the firmware utilized to conduct components initialization in the course of the booting course of action) to access out to Dell backend products and services more than the internet. Then, it coordinates an update or recovery system.
The issue is that the TLS relationship applied to join BIOS to the backend servers will take any legitimate wildcard certification, Eclypsium scientists said. So, an attacker with a privileged network posture can intercept that relationship, impersonate Dell and deliver attacker-managed content back to the target system.
“The approach of verifying the certificate for dell.com is performed by 1st retrieving the DNS document from the tricky-coded server 8.8.8.8, then setting up a link to [Dell’s download site],” according to the examination. “However, any valid wildcard certificate issued by any of the constructed-in Certification Authorities contained in the BIOSConnect characteristic in BIOS will satisfy the safe connection situation, and BIOSConnect will commence to retrieve the applicable data files. The bundle of CA root certificates in the BIOS picture was sourced from Mozilla’s root certification file (certdata.txt).”
Overflow Vulnerabilities Enabling Arbitrary Code Execution
Once this to start with “gatekeeper” bug is exploited to deliver destructive information again to the target equipment, attackers then have a decision of three distinct and impartial overflow vulnerabilities (CVE-2021-21572, CVE-2021-21573, CVE-2021-21574), any of which can be utilized to acquire pre-boot RCE on the goal gadget, scientists reported.
Two of the vulnerabilities have an impact on the OS recovery course of action, whilst the third affects the firmware update process, in accordance to Eclypsium, which is not releasing further more complex aspects yet.
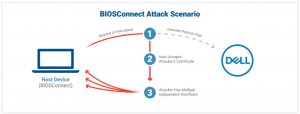
The attack scenario: Click on to enlarge. Resource: Eclypsium
Any attack scenario would need an attacker to be equipped to redirect the victim’s traffic, this sort of as by way of a equipment-in-the-center (MITM) attack – anything that’s not a lot of a barrier, researchers said.
“Machine-in-the-center attacks are a rather low bar to refined attackers, with tactics this kind of as ARP spoofing and DNS cache poisoning remaining very well-recognized and quickly automatic,” in accordance to the report. “Additionally, business VPNs and other network equipment have become a top rated concentrate on of attackers, and flaws in these products can allow attackers to redirect visitors. And finally, close-users functioning from house are increasingly reliant on SOHO networking gear. Vulnerabilities are fairly widespread in these types of buyer-grade networking units and have been exploited in popular strategies.”
The groundwork work to have out an attack is probably a optimistic tradeoff for cybercriminals, reported, presented that a successful compromise of the BIOS of a product would make it possible for attackers to set up ongoing persistence while controlling the greatest privileges on the system. This is mainly because they would command the course of action of loading the host running technique, and would be capable to disable protections in get to remain undetected, the report pointed out.
“The almost endless manage above a system that this attack can deliver helps make the fruit of the labor properly really worth it for the attacker,” Eclypsium scientists claimed.
Dell Issues Patches
Dell is starting off to press out patches for BIOS on all of the affected systems, with most updates scheduled for Thursday, and some others to abide by in July, it reported in its advisory.
“It is advisable to operate the BIOS update executable from the OS after manually examining the hashes against individuals released by Dell,” Eclypsium advised, fairly than relying on BIOSConnect to use BIOS updates.
Be part of Threatpost for “Tips and Methods for Much better Threat Hunting” — a Live party on Wed., June 30 at 2:00 PM ET in partnership with Palo Alto Networks. Understand from Palo Alto’s Device 42 professionals the very best way to hunt down threats and how to use automation to enable. Register HERE for cost-free!
Some elements of this posting are sourced from:
threatpost.com

 Antivirus creator John McAfee found dead in Spanish prison
Antivirus creator John McAfee found dead in Spanish prison