New research into 5G architecture has uncovered a security flaw in its network slicing and virtualized network features that could be exploited to enable info obtain and denial of services attacks in between different network slices on a cellular operator’s 5G network.
AdaptiveMobile shared its results with the GSM Affiliation (GSMA) on February 4, 2021, next which the weaknesses have been collectively designated as CVD-2021-0047.
5G is an evolution of current 4G architectures and is primarily based on what’s called a provider-dependent architecture (SBA) that provides a modular framework to deploy a established of interconnected network features, letting people to find and authorize their entry to a plethora of products and services.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The network capabilities are also responsible for registering subscribers, running sessions and subscriber profiles, storing subscriber data, and connecting the customers (UE or user gear) to the internet by means of a base station (gNB). What is actually a lot more, every network operate of the SBA can provide a precise services but at the identical time can also ask for a support from yet another network functionality.
A person of the approaches the core SBA of the 5G network is orchestrated is by way of a slicing model. As the identify implies, the concept is to “slice” the first network architecture in multiple reasonable and independent digital networks that are configured to fulfill a particular company purpose, which, in flip, dictates the quality of provider (QoS) necessities vital for that slice.
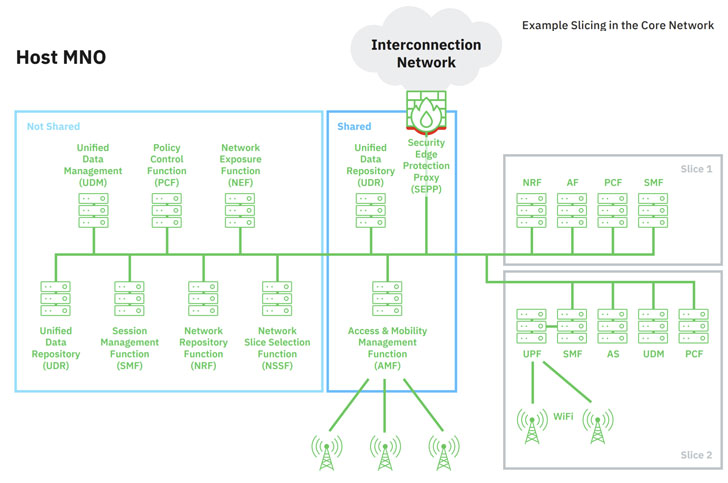
On top of that, every slice in the main network is made up of a rational team of network features (NFs) that can be exclusively assigned to that slice or be shared among the different slices.
Set in different ways, by building separate slices that prioritize selected traits (e.g., significant bandwidths), it allows a network operator to carve out methods that are customized to specific industries.
For occasion, a mobile broadband slice can be made use of to aid leisure and Internet-relevant providers, an Internet of Issues (IoT) slice can be used to supply products and services tailor-made to retail and manufacturing sectors, while a standalone small latency slice can be designated for mission-critical wants these as health care and infrastructure.
“The 5G SBA presents a lot of security features which features lessons discovered from previous generations of network technologies,” AdaptiveMobile stated in a security investigation of 5G core network slicing. “But on the other hand, 5G SBA is a totally new network strategy that opens the network up to new associates and solutions. These all guide to new security worries.”
In accordance to the cell network security firm, this architecture not only poses contemporary security worries that stem from a have to have to guidance legacy features but also from a “huge boost in protocol complexity” as a consequence of migrating from 4G to 5G and in the procedure opening the door to a multitude of attacks, together with —
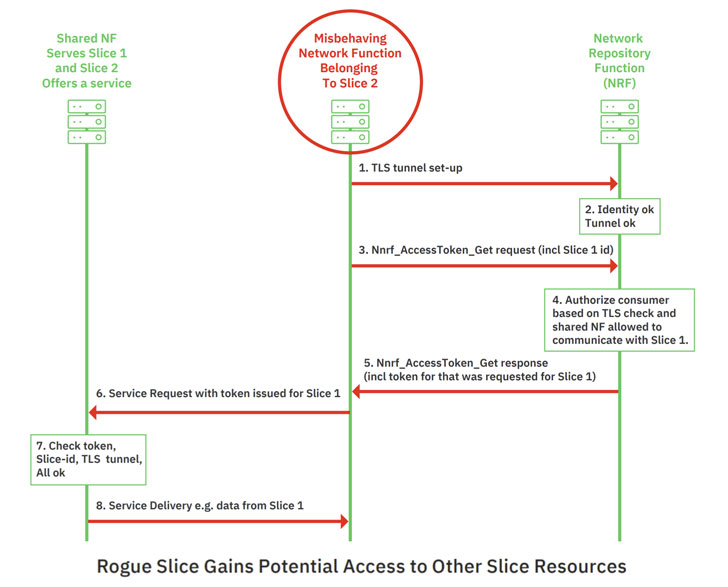
- Malicious entry to a slice by brute-forcing its slice differentiator, an optional price set by the network operator for distinguishing among slices of the identical variety, thus enabling a rogue slice to gain unauthorized facts from a 2nd slice like Entry and Mobility Administration Functionality (AMF), which maintains knowledge of a consumer equipment’s spot.
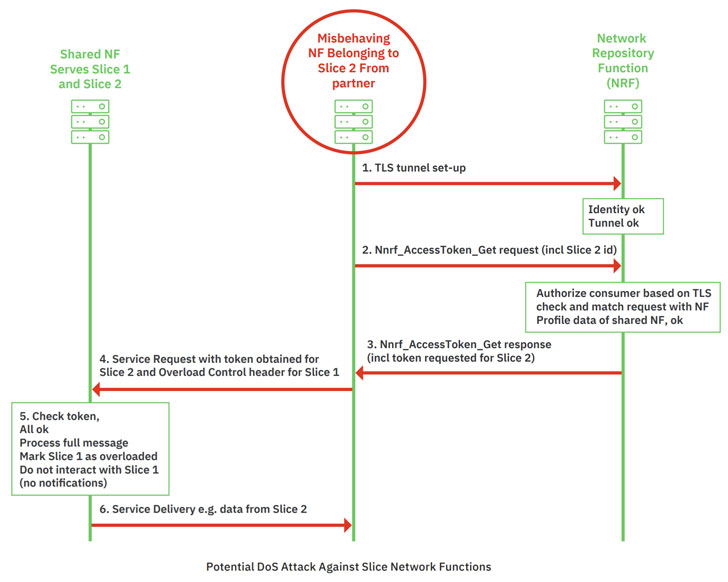
- Denial-of-services (DoS) towards yet another network function by using edge of a compromised slice.
The attacks hinge on a design and style quirk that there are no checks to guarantee that the slice identity in the signaling layer ask for matches that used in the transportation layer, therefore allowing an adversary related to the 5G operator’s SBA by way of a rogue network operate to get keep of the core network as nicely as the network slices.
It truly is worth noting that the signaling layer is the telecommunication-unique software layer made use of for exchanging signaling messages concerning network capabilities that are positioned in various slices.
As countermeasures, AdaptiveMobile endorses partitioning the network into distinctive security zones by making use of signaling security filters among unique slices, the main network, and exterior partners, and shared and not-shared network capabilities network, in addition to deploying a signaling layer security remedy to safeguard versus data leakage attacks that leverage the lacking correlation between layers.
Although the present-day 5G architecture would not support these kinds of a defense node, the research indicates improving the Services Conversation Proxy (SCP) to validate the correctness of message formats, match the details in between layers and protocols, and give load-relevant operation to avert DoS attacks.
“This form of filtering and validation approach makes it possible for division of the network into security zones and safeguarding of the 5G main network,” the researchers reported. “Cross-correlation of attack information amongst those people security network capabilities maximizes the defense against refined attackers and lets much better mitigations and quicker detection while minimizing wrong alarms.”
Uncovered this article attention-grabbing? Observe THN on Facebook, Twitter and LinkedIn to browse a lot more exceptional written content we post.
Some elements of this post are sourced from:
thehackernews.com


 Another Critical RCE Flaw Discovered in SolarWinds Orion Platform
Another Critical RCE Flaw Discovered in SolarWinds Orion Platform